If you’ve ever been to Cisco Live and seen the booth with a display for you to pick locks, then you know about the Cisco Advanced Security Initiatives Group (ASIG). We are chartered with security testing and ethical hacking for all Cisco products and services, whether in the cloud or on-premises. Anything Cisco sells, we have a go at it and try to break it—finding vulnerabilities as early as possible—before it’s deployed on the internet and reaches customer environments.
Our Product Security Incident Response Team (PSIRT) distributes information about discovered vulnerabilities to help harden Cisco offerings. If you have a vulnerable scenario, learning how to exploit these vulnerabilities in a network could help you determine what mitigations to apply and strengthen your security posture.
Becoming a Hacker
Every year, we have a class called Becoming a Hacker, which teaches students how to ethically hack into a simulated network so they can learn how to protect it. It’s mainly for interns from colleges and high schools involved in cybersecurity studies.
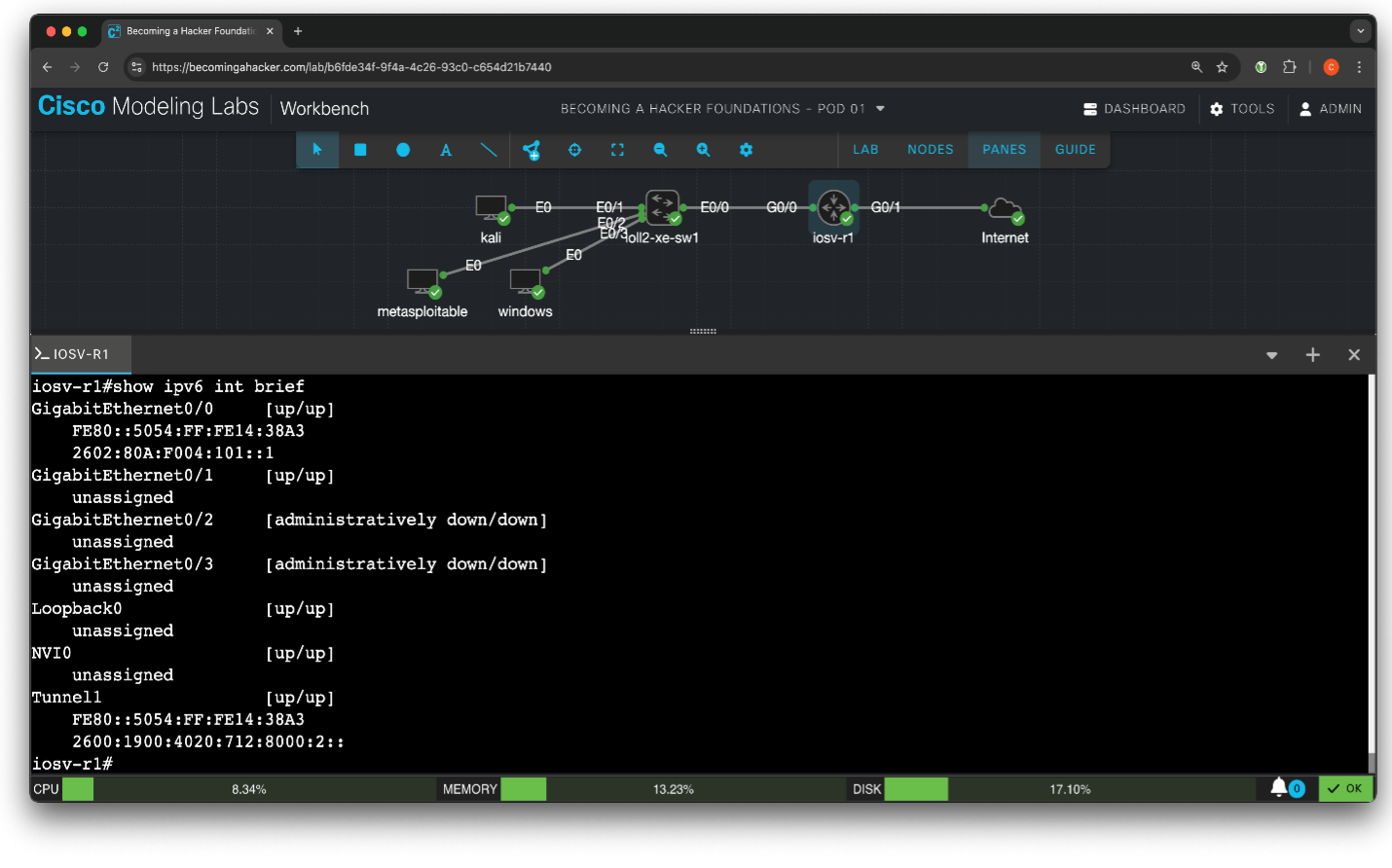
The Becoming a Hacker course gives students exposure to a real-world network (using Cisco Modeling Labs [CML]). This simulated network acts more like what they would see on-premises, using physical switches, routers, and firewalls. Cloud networks are typically more locked down (rightly so) and behave differently. Becoming a Hacker also features a simulated Wi-Fi network, so students get exposed to various network types. We plan to have cloud targets in the Becoming a Hacker lab eventually, so the students will have a blend of virtual on-prem and in-cloud targets, getting the best of both worlds.
Becoming a Hacker has recently become public, so anyone can access the course materials via Github. Of course, we do not make the CML web interface public for security reasons, but we can quickly take it down and start it back up at scale.
While Becoming a Hacker is created by volunteers and is not an official Cisco product, it does provide a great starting point for customers who want to create their own hacker training scenarios using a cloud account.
How a network hacking course can teach network protection
A course on ethical hacking, also known as penetration testing or white-hat hacking, is crucial for companies in the long run, helping them identify and fix vulnerabilities before malicious hackers can exploit them, thus strengthening the network against future attacks. Training in ethical hacking can also help companies comply with security regulations and save money, avoiding the cost of legal fees, fines, and business loss from data breaches. Overall, this kind of training improves security awareness throughout the organization, leading to better security policies and training for employees to help them recognize and respond to potential threats.
The premise is that when you engineer something to be secure, you must learn to break it. That way, you will know what to look for within your own networks. A common finding is an OS command injection vulnerability, a web vulnerability in which the attacker uses existing APIs to execute arbitrary code by tacking on an additional operating system command using special characters.
One example is a web interface that allows you to ping a host so you can confirm reachability through that web interface, which may allow those characters to execute commands other than a ping. When you understand the kind of damage a hacker can do to your network, you can better understand the criticality of defending it.
Working with Cisco Modeling Labs for more open training
Lately, we’ve been working with the CML team for Cisco’s internal training, which lets our ethical hackers use CML to do security testing for every Cisco product. However, what started as a private project is turning into a potentially significant opportunity for an open-source solution.
It’s an entirely different way of building a network so that you can do offensive security testing. We’ve been running it in Google Cloud, and it’s working great.
Cisco Modeling Labs deployment in the Google Cloud platform
We’ve been using examples of Terraform configurations on DevNet. These configurations allow you to take the CML image generally provided as an ISO image or application package and cloudify it for installation in Amazon Web Services (AWS) or Microsoft Azure. Terraform is a tool for defining and managing IT infrastructure using code, or infrastructure as code (IaC). IaC makes it easier to set up, update, and scale your resources consistently and efficiently.
While that was working well, we soon realized that to run it at the scale we needed, we would have to run CML on more than one bare-metal machine in a cluster in AWS—and that gets expensive. We also required that each lab could accept connections from the Internet and initiate connections to the Internet with IPv4 and IPv6 using unique addresses. We found that the Google Cloud Platform met our needs nicely.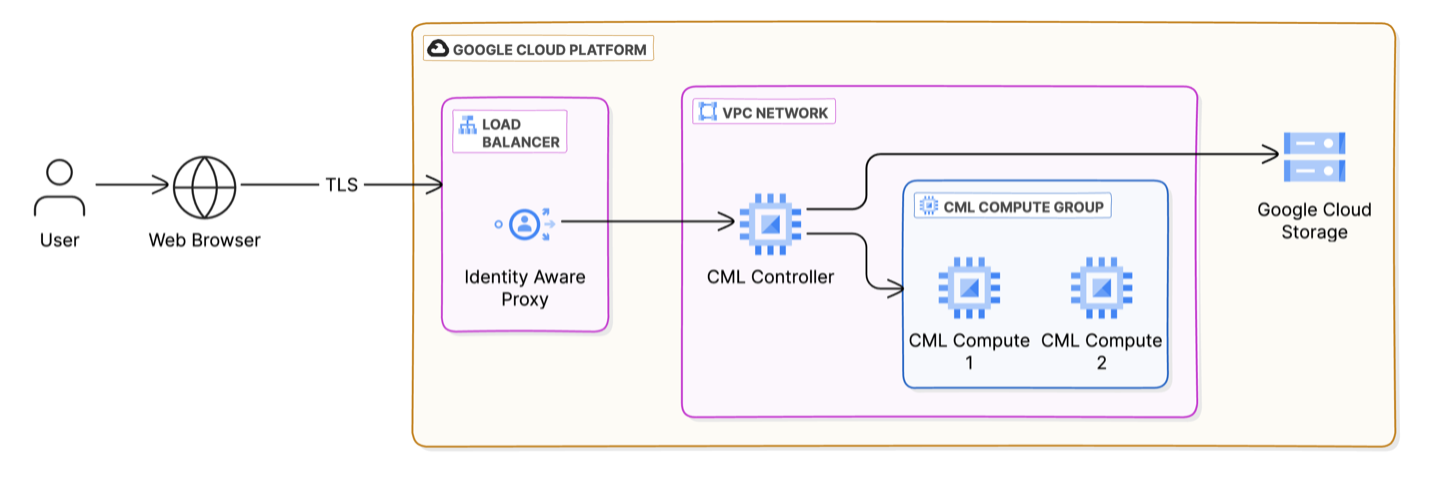 CML runs its own hypervisor, which is software that allows a single computer to run several virtual machines (VMs) simultaneously. The hypervisor is a security measure.*
CML runs its own hypervisor, which is software that allows a single computer to run several virtual machines (VMs) simultaneously. The hypervisor is a security measure.*
CML’s open-source hypervisor is based on Linux Kernel-based virtual machine (KVM) and libvirt, a toolkit to manage virtualization platforms. It allows you to run virtual machines on server hardware like the Cisco Unified Computing System (UCS). This CML hypervisor can run nested on virtual machine instances in the cloud and run virtual machines by itself to support our labs.
Cisco Modeling Labs workbench interface
By taking this course with CML, users connecting remotely with a web browser will get their own pod (a group of virtual, exploitable machines). And since it’s been working so well for our internal teams, the CML team was agreeable when I offered to write the Terraform modules to use Google Cloud Platform to expand our training.
I hope to document a Google Cloud deployment and integrate these changes into the main DevNet repository soon.
Becoming a Hacker lab deployment
We want to make this method of provisioning labs for training more universal. The Becoming a Hacker Foundations course is the first iteration of this method. We also offer other cybersecurity classes internally, but none use CML… yet.
Because CML allows you to interface from anywhere, you can access your CML instance on the cloud and do testing. It’s so compelling to use because it’s all automated.
For example, when we run a Terraform command, 20 pods (virtualized labs) are ready for use. We have all the configs to deploy it if you have a CML subscription. While not all of the images are fully public because it has a licensed Windows image, a user could easily create their own images not provided out-of-the-box.
We hope to expand this course over time. Stay tuned for more info on this great opportunity for Cisco training and CML to help you learn more hacking tips and tricks to better secure your network.
NOTE: Cisco Modeling Labs is a commercial and officially supported product from Cisco. Learn more
Sign up for Cisco U. | Join the Cisco Learning Network.
Follow Cisco Learning & Certifications
X | Threads | Facebook | LinkedIn | Instagram | YouTube
Use #CiscoU and #CiscoCert to join the conversation.
*How we secure the Becoming a Hacker course
There’s no vulnerability in Cisco Modeling Labs (CML) that we know of, but we’re deploying a lab (pod) that has devices in it that are vulnerable. CML allows you to make a networking topology, not only for routers but also for servers and hosts. You can deploy a Linux or Windows machine into it. It’s all based on a kernel-based virtual machine (KVM), a virtualization technology that turns a Linux machine into a hypervisor, allowing multiple isolated virtual environments to run on a single host machine.
Hypervisors are critical to the security of virtualized environments, especially if you run machines that might execute vulnerable code. Some important ways hypervisors address security include:
- Isolating virtual machines (VMs) from each other ensures that if one VM is compromised, the attacker cannot easily access other VMs (which contain known vulnerable code) or the host system.
- Controlling allocating hardware resources (CPU, memory, storage, and network) to VMs to prevent resource exhaustion, where one student lab can overload others.
- Enforcing strict access control policies so only authorized users and processes can interact with the VMs and the hypervisor itself, so students only see their virtual machines and not others.
- Implementing virtual network security measures, such as virtual firewalls and network segmentation, to protect VMs from network-based attacks.
- Sandboxing VMs to limit their ability to interact with the host system and other VMs.
Here are a few other security measures we use for our Becoming a Hacker site:
- We isolate the site from the rest of Cisco, which is one reason it’s important to run CML in the cloud. If something were to happen, we could quickly destroy the deployment and recreate it. However, if this were running deep inside a Cisco lab, that would be more difficult and might harm Cisco’s corporate network.
- We protect the site with strong passwords generated during lab creation and multifactor authentication (such as Duo) using the Identity Aware Proxy, which can also be turned off and on depending on the class’s audience.
- While the lab has free access to the Internet, its speed is limited; each pod can only transmit a few megabits per second.
- We keep Domain Name Service (DNS) and flow logs of people’s actions across the network.
- Every pod has a unique IP address, which we can trace to individual students.
Secure Organizations by Thinking Like a Hacker
Exploring AAA and TACACS Configuration with Cisco Modeling Labs
Share: